A stable connection between the home office or remote infrastructures and the company network must ensure a good balance between performance and security. This requires a combination of several technological solutions to be optimally aligned with the individual security and process requirements of the organization.
Whether in the home office or at a mobile workplace, employees today need to be able to access their company’s IT systems around the clock. Prerequisites for a secure home office and for IT security while on the road are the protection of the company network against compromised private systems and a systematic separation of private and business data. genua offers an extensive line of products for remote work that can be combined to create individual solutions.
VPN Software Client genuconnect
When working remotely with classified information, a highly secure connection to the company’s network is imperative. This protection is provided by the VPN software client genuconnect for laptops and tablets with Windows 10 or 11. genconnect is approved for the classification levels German VS-NfD, RESTREINT UE/EU RESTRICTED, and NATO RESTRICTED.
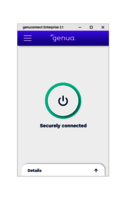
VPN Software Client genuconnect Enterprise
genuconnect Enterprise provides your organization with a security level comparable to approved solutions. The VPN software client connects remote employees easily and reliably to company networks. And if your security needs increase: simply switch to the approved genuconnect version.
ECOS SecureBootStick SX
With the combination of the genuscreen VPN solution and the ECOS SecureBootStick SX, genua and ECOS offer maximum protection for the exchange of confidential data in remote operation or in the home office. This can be used extremely flexibly, allowing employees to, for example, even use a private laptop to access information classified as restricted.
Workshops & Trainings
With the knowledge and practical application experience from our training courses, you can properly use and administer our products.
Services
Service for our IT security solutions is provided directly by genua or our trained sales partners.
Still haven’t found what you’re looking for?
Discover all of genua’s solutions
genua’s products and services protect the exchange of information in the areas with the highest demands on IT security. Learn more about our service portfolio.
Knowledge Base
As a collaborative learning company, it is our mission to continuously improve and share our knowledge of IT Security with you. In our Knowledge Base we offer you articles, white papers, analyst reports, research results, videos and more in the field of IT security.
Public Sector
- Remote Maintenance in Networks with Classification Level "German VS-NfD": Mixed-Reality Collaboration in Real Time for German Armed Services and Defense Technology
- Speed is the Key Factor – Not Hundred-Percent Security
- ELSTER, German Federal States Electronic Tax System
- Remote Maintenance for Critical Infrastructure: Made Possible through Security